Generating 2048 Bit Rsa Keys Keys Will Be Non-exportable
15.12.2020 admin
- October 2, 2015
- Posted by: Syed Shujaat
- Category: Cisco, Networking Solutions
Aug 14, 2009 bgprouter(config)#crypto key generate rsa general-keys modulus 2048 The name for the keys will be: bgprouter.router.uq.edu.au% The key modulus size is 2048 bits. Aug 14, 2009 bgprouter(config)#crypto key generate rsa general-keys modulus 2048 The name for the keys will be: bgprouter.router.uq.edu.au% The key modulus size is 2048 bits. We need configure SSH on a Cisco router or switch in order to access it remotely, unless we’re using an access server. C1801% The key modulus size is 1024 bits% Generating 1024 bit RSA keys, keys will be non-exportable.OK C1801(config). Crypto key generate rsa modulus 1024 label C1801: Generating a certificate.
Use this command to generate RSA key pairs for your Cisco device (such as a router). keys are generated in pairs–one public RSA key and one private RSA key.
If your router already has RSA keys when you issue this command, you will be warned and prompted to replace the existing keys with new keys.
NOTE: Before issuing this command, ensure that your router has a hostname and IP domain name configured (with the hostname and ipdomain-name commands).
You will be unable to complete the cryptokeygeneratersacommand without a hostname and IP domain name. (This situation is not true when you generate only a named key pair.)
Here are the steps to Enable SSH and Crypto Key setup : 2 config must requried for SSH
1 Setup Local VTY line User ID and password
router (Config) # Line VTY 0 15
router (Config-line)# login local
router (Config-line)# Exit
!!! create local login ID/Pass
router (Config)# username [loginid] password [cisco]
router (Config)# username loginid1 password cisco1
2. router (Config)# ip domain-name example.com
router (Config)# crypto key generate rsa
how many bits in the modulus [512] :1024
router (Config)# ip ssh version2
router (Config)# CTRL Z
Note | Secure Shell (SSH) may generate an additional RSA key pair if you generate a key pair on a router having no RSA keys. The additional key pair is used only by SSH and will have a name such as {router_FQDN }.server. For example, if a router name is “router1.cisco.com,” the key name is “router1.cisco.com.server.” |
This command is not saved in the router configuration; however, the RSA keys generated by this command are saved in the private configuration in NVRAM (which is never displayed to the user or backed up to another device) the next time the configuration is written to NVRAM.
Modulus Length
When you generate RSA keys, you will be prompted to enter a modulus length. The longer the modulus, the stronger the security. However, a longer modules take longer to generate (see the table below for sample times) and takes longer to use.
The size of Key Modulus range from 360 to 2048. Choosing modulus greater than 512 will take longer time.
| Router | 360 bits | 512 bits | 1024 bits | 2048 bits (maximum) |
|---|---|---|---|---|
| Cisco 2500 | 11 seconds | 20 seconds | 4 minutes, 38 seconds | More than 1 hour |
| Cisco 4700 | Less than 1 second | 1 second | 4 seconds | 50 seconds |
Cisco IOS software does not support a modulus greater than 4096 bits. A length of less than 512 bits is normally not recommended. In certain situations, the shorter modulus may not function properly with IKE, so we recommend using a minimum modulus of 2048 bits.
Syntax Description : Optional Strings to embed with SSH Crypto key
| general-keys | (Optional) Specifies that a general-purpose key pair will be generated, which is the default. | ||
| usage-keys | (Optional) Specifies that two RSA special-usage key pairs, one encryption pair and one signature pair, will be generated. | ||
| signature | (Optional) Specifies that the RSA public key generated will be a signature special usage key. | ||
| encryption | (Optional) Specifies that the RSA public key generated will be an encryption special usage key. | ||
| labelkey-label | (Optional) Specifies the name that is used for an RSA key pair when they are being exported.If a key label is not specified, the fully qualified domain name (FQDN) of the router is used. | ||
| exportable | (Optional) Specifies that the RSA key pair can be exported to another Cisco device, such as a router. | ||
| modulusmodulus-size | (Optional) Specifies the IP size of the key modulus.By default, the modulus of a certification authority (CA) key is 1024 bits. The recommended modulus for a CA key is 2048 bits. The range of a CA key modulus is from 350 to 4096 bits.
| ||
| storagedevicename: | (Optional) Specifies the key storage location. The name of the storage device is followed by a colon (:). | ||
| redundancy | (Optional) Specifies that the key should be synchronized to the standby CA. | ||
| ondevicename: | (Optional) Specifies that the RSA key pair will be created on the specified device, including a Universal Serial Bus (USB) token, local disk, or NVRAM. The name of the device is followed by a colon (:).Keys created on a USB token must be 2048 bits or less. |
| Command | Description |
|---|---|
| copy | Copies any file from a source to a destination, use the copy command in privileged EXEC mode. |
| cryptokeystorage | Sets the default storage location for RSA key pairs. |
| debugcryptoengine | Displays debug messages about crypto engines. |
| hostname | Specifies or modifies the hostname for the network server. |
| ipdomain-name | Defines a default domain name to complete unqualified hostnames (names without a dotted-decimal domain name). |
| showcryptokeymypubkeyrsa | Displays the RSA public keys of your router. |
| show crypto pki certificates | Displays information about your PKI certificate, certification authority, and any registration authority certificates. |
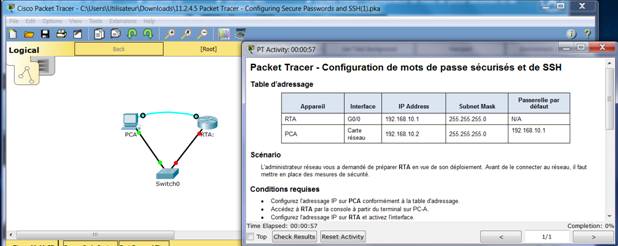
Introduction
This document describes the configuration example of Session Initiation Protocol (SIP) Transport Layer Security (TLS) and Secure Real-time Transport Protocol (SRTP) between Cisco Unified Communications Manager (CUCM), IP phone and Cisco Unified Border Element (CUBE) with the use of Enterprise Certificate Authority (CA) (Third Party CA) Signed certificates and to use common Enterprise CA to sign certificates for all network components which includes Cisco Communications devices like IP phones, CUCM, Gateways and CUBEs.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- Enterprise CA server is configured
- CUCM Cluster is configured in Mixed mode and IP Phones are registered in Secure Mode (Encrypted)
- CUBE basic voice service VoIP and dial-peer configuration is done
Components Used
The information in this document is based on these software and hardware versions:
- Windows 2008 server - certificate authority
- CUCM 10.5
- CUBE - 3925E with Cisco IOS® 15.3(3) M3
- CIPC
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Background Information
Secure voice communication over CUBE can be divided into two parts
- Secure Signaling - CUBE use TLS to secure signaling over SIP and Internet Protocol Security (IPSec) in order to secure signaling over H.323
- Secure Media - Secure Real-time Transport Protocol (SRTP)
CUCM Certificate Authority Proxy Function (CAPF) provides Locally Significant Certificate (LSC) to phones. So when CAPF is signed by external CA, it would act as subordinate CA for the phones.
In order to understand how to get CA-Signed CAPF, refer to:
Configure
Network Diagram
In this setup, Root CA and one Subordinate CA are used. All CUCM and CUBE certificates are signed by Subordinate CA.
Configure CUBE
Generate an RSA Keypair.
This step generates Private and Public Keys.
In this example, CUBE is just a Label, this can be anything.
2. Create a trustpoint for Subordinate CA and Root CA, Subordinate CA trustpoint is used for SIP TLS communication.
In this example, trustpoint name for subordinate CA is SUBCA1 and for Root CA it is ROOT.
Subject name used in this step must match on X.509 Subject Name on CUCM SIP Trunk security profile. Best practice is to use host-name with domain name (if domain name is enabled).
Associate RSA Key pair created in Step 1.
3. Generate CUBE Certificate Signing Request (CSR).
The crypto pki enroll command produces the CSR that is provided to the Enterprise CA in order to get the signed certificate.
Copy the output between BEGIN CERTIFICATE REQUEST to END CERTIFICATE REQUEST and save it in notepad file.
CUBE CSR would have these Key attributes:
4. Get CA certificate root CA, then CA certificate and Signed CUBE certificate from Subordinate CA.
In order to get Signed CUBE certificate, use CSR generated in Step 3. The image is from Microsoft CA web server.
5. Import CA certificate of Root CA and Subordinate CA.
Generating 2048 Bit Rsa Keys Keys Will Be Non-exportable Full
Open Certificate in notepad and copy-and-paste content from BEGIN CERTIFICATE REQUEST to END CERTIFICATE REQUEST.
6. Import CUBE signed Certificate.
Open Certificate in notepad and copy-and-paste content from BEGIN CERTIFICATE REQUEST to END CERTIFICATE REQUEST.
How To Generate Rsa Key
7. Configure TCP TLS as transport protocol.
This can be done either at global or at dial-peer level.
8. Assign trustpoint for sip-ua, this trustpoint would be used for all sip signaling between CUBE and CUCM:
or, default trustpoint can be configured for all sip signaling from cube:
9. Enable SRTP.
This can be done either at global or at dial-peer level.
10. For SRTP and Real-time Transport Protocol (RTP) internetworking, secure transcoder is required.
If Cisco IOS® version is 15.2.2T (CUBE 9.0) or later then, Local Transcoding Interface (LTI) transcoder can be configure to minimize the configuration.
LTI transcoder doesn't need Public Key Infrastructure (PKI) trustpoint configuration for SRTP-RTP calls.
If Cisco IOS® is below 15.2.2T, then configure SCCP transcoder.
SCCP transcoder would need trustpoint for signaling, however, if same router is used to host the transcoder then same trustpoint (SUBCA1) can be used for CUBE as well as transcoder.
Configure CUCM
1. Generate CallManager CSR on all CUCM nodes.
Generating 1024 Bit Rsa Keys Keys Will Be Non-exportable
Navigate to CM OS Administration > Security > Certificate Management > Generate Certificate Signing Request as shown in the image.
CallManager CSR would have these Key attributes:

2. Get CallManager certificate for all CM nodes signed by subordinate CA.
Use CSR generated in Step 1. Any web-server certificate template would work, ensure that the Signed Certificate have atleast these Key Usage attributes: Digital Signature, Key Encipherment, Data Encipherment as shown in the image.
3. Upload CA certificate from Root CA and Subordinate CA as CallManager-Trust.
Navigate to CM OS Administration > Security > Certificate Management > Upload Certificate/Certificatechain as shown in the images.
4. Upload CallManager Signed certificate as CallManager as shown in the image.
5. Update Certificate Trust List (CTL) file on Publisher (through CLI).
6. Restart CallManager and TFTP service on all nodes and CAPF service on Publisher.
7. Any video converter professional key generator. Create New SIP Trunk Security Profile.
Generating 2048 Bit Rsa Keys Keys Will Be Non-exportable Chords
On CM Administration, navigate to System > Security > SIP Trunk Security Profiles > Find.
Copy existing Non Secure SIP Trunk Profile to create new secure profile as shown in this image.
8. Create SIP trunk to the CUBE.
Enable SRTP Allowed on SIP trunk as shown in the image.
Configure Destination port 5061 (TLS) and apply New Secure SIP trunk Security profile on the SIP trunk as shown in the image.
Verify
Use this section in order to confirm that your configuration works properly.
Generating 2048 Bit Rsa Keys Keys Will Be Non-exportable Today
The output of show call active voice brief command is captured when LTI transcoder is used.
Also, when SRTP encrypted call is made between Cisco IP phone and CUBE or Gateway, a lock icon is displayed on the IP phone.
Troubleshoot
Generating 2048 Bit Rsa Keys Keys Will Be Non-exportable Lyrics
This section provides information you can use in order to troubleshoot your configuration.
These debugs would be helpful for troubleshooting PKI/TLS/SIP/SRTP issues.